What is data Protection
Overview
People have the right to privacy. It is a fundamental human right and this extends to data in the form of a persons personal information. Data protection is about safeguarding this right and applies to governments, organisations and companies that store personal information on those that use or access their products or services. Generally information is regarded as personal if the data can identify the living individual, whether in personal or family life, business or profession.
Where a body of law on data protection exists it will require, amongst other things, that the information you keep on your clients/beneficiaries be secure. And where no legal frame work exists you should be guided by ethics- afford others the level of data protection you would expect for yourself.
Data Protection Law
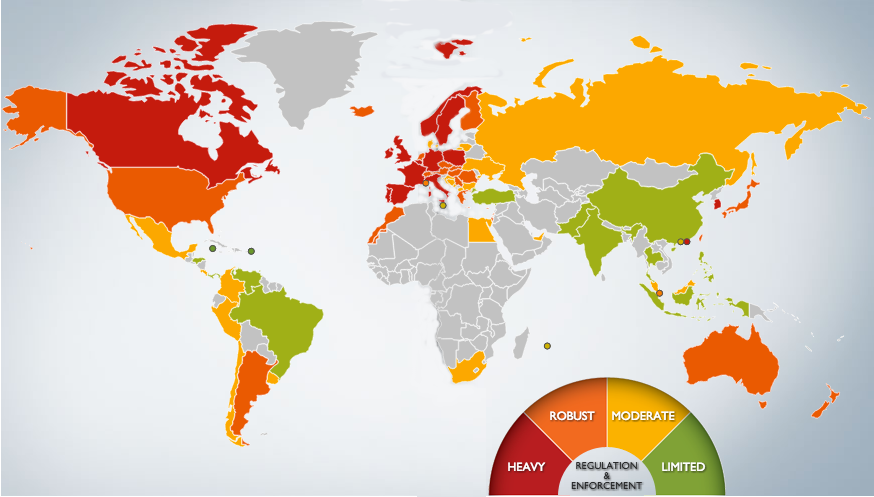
Well over a hundred countries around the world have data protection laws and yearly the number grows.
Data Protection & Mobile Systems
Moving from storing data locally on spread sheets or databases to data collected and stored remotely brings with it a responsibility for data protection. If a mobile device is lost or stolen your beneficiaries should be confident their personal information is protected. And, if your database is targeted, they should also be assured you made every reasonable effort to protect them.
Such risks should be self evident. Data protection is based on law or, in its absence, ethics and not how valuable or invaluable you think your clients data may be to an unscrupulous third party.
Basic Data Protection & Design

In traditional spread sheet based systems data was inaccessible to outside parties. With web or mobile platforms this is no longer the case.
Components of Security
Many companies face the challenge of retrospectively adding security to existing systems. But, if you are planning a new system it should be a design consideration from the start. M&E systems should be specified to meet a basic level of data protection. And this requires that consideration be given to how data is stored, transmitted and accessed.
Security is a combination of elements
How you store, transmit and access your clients data determines how well you will protect their right to privacy.
Transmitting data securely
For transmitted data you should specify HTTPS. This simply means the web address you will use for the system will have an SSL certificate installed. This is simple, very inexpensive and the single easiest step you can take.
Consider specifying certified connections

We are all familiar with secure connections and have come to expect them on sites where we send sensitive information.
Accessing data securely
Data access and storage is slightly more complicated but can be simplified into organisation policy and system design. Ultimately it is the combination of a secure system in a secure working environment that delivers effective security.
Working environments are notoriously difficult when it comes to securing access to data. Staff need to have and maintain passwords and these are often kept on post-it notes, based on birth dates, or simply generated from the text 'password'. Typically, threat appreciation is low because few organizations will have in place a policy that covers data security and few will have briefed their staff on the basics.
Organisation Policy

Generally staff take their lead on security from the organisation they work for.
Storing data securely
It is likely you will depend on a service provider for your data storage and so ultimately on their security also. But, for your administrator access, you must be prepared to employ 16 - 24 alpha/numeric passwords changeable on a regular basis.
A step further than this could be to employ encryption on some of the clients data such as cell number and surname. Data encryption (depending on your platform) can be very straight forward computationally but it carries with it a significant added administrative responsibility.
The one big disadvantage of encryption is it relates to keys so that the security of data becomes the security of the encryption key. This means lose the key, and you effectively lose your data. This, and the issues with system performance require a compelling case for deployment typically only found on projects with sexual/reproductive health or micro finance component.
Don't lose the key...

Encrypted data is accessed through a single key. Administration of this is the greatest challenge in adopting this level of security.
